By Boluwatife, Technology Correspondent | April 16, 2026
This explainer draws from the full investigation and exclusive Q&A conducted by David Odes (@chiefdavidsays), Cybersecurity & Privacy Researcher, Speaker and Instructor, and Founder of Web Security Lab.
- ByteToBreach reveals opportunistic breaches at Sterling Bank, Remita and CAC using known vulnerabilities and misconfigurations
- CAC registry compromised via sequential user IDs, JWT token generation flaw and unauthenticated file downloads on public subdomain
- Sterling Bank negotiated €250,000 ransom with threat actor but couldn’t stop data publication after repeated delays while customers remained uninformed
MAIN STORY
On April 15 at 5:03am, cybersecurity researcher David Odes, founder of WebSecurityLab and known on X as @chiefdavidsays, sent 10 questions to the contact address published by threat actor ByteToBreach. The questions covered the Sterling Bank and Remita breaches, the newly reported Corporate Affairs Commission incident, potential data modification, human consequences, and whether the affected organisations had been contacted before data publication.
ByteToBreach responded the same day—the same day the Corporate Affairs Commission issued its first public statement acknowledging the breach. Two institutions, one criminal and one governmental, went on record within hours of each other. This is what they said, what it means, and what it reveals about Nigeria’s third major institution hit in the actor’s recent operations.
The pattern is clear. ByteToBreach finds an open door, documents everything inside with methodical patience, and publishes. The first door was an unpatched vulnerability (CVE-2025-55182) on Sterling Bank’s pilot server enf-pilot.sterling.ng. The second was Remita’s Git repository with plaintext credentials in production configuration files. The third was the CAC.
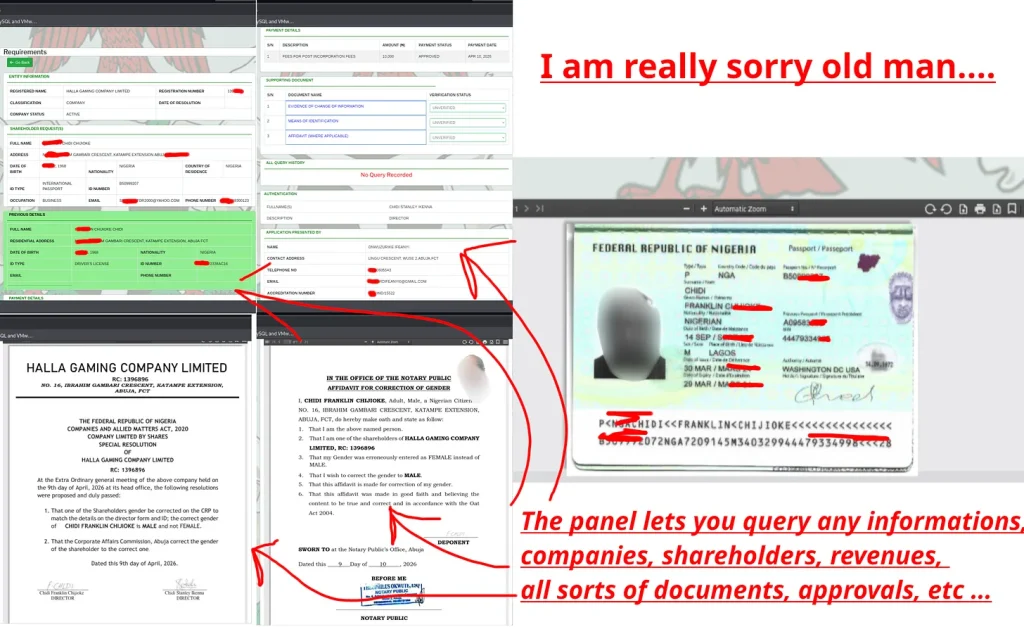
Most Nigerians know the Corporate Affairs Commission as the agency for company registration—pay the fees, submit forms, receive an RC number. That description is accurate as far as it goes. In reality, the CAC maintains the authoritative legal record of every company, business name, and incorporated trustee in Nigeria: directors, shareholders, registered addresses, changes of ownership, board resolutions, and every piece of identity documentation submitted for verification.
Banks rely on CAC data for due diligence. Courts use it to establish ownership. The EFCC pulls records during investigations. Contracts turn on who actually controls an entity according to the CAC registry. It is foundational infrastructure—the ground truth of Nigerian corporate identity. If the information is wrong, every dependent system is compromised.
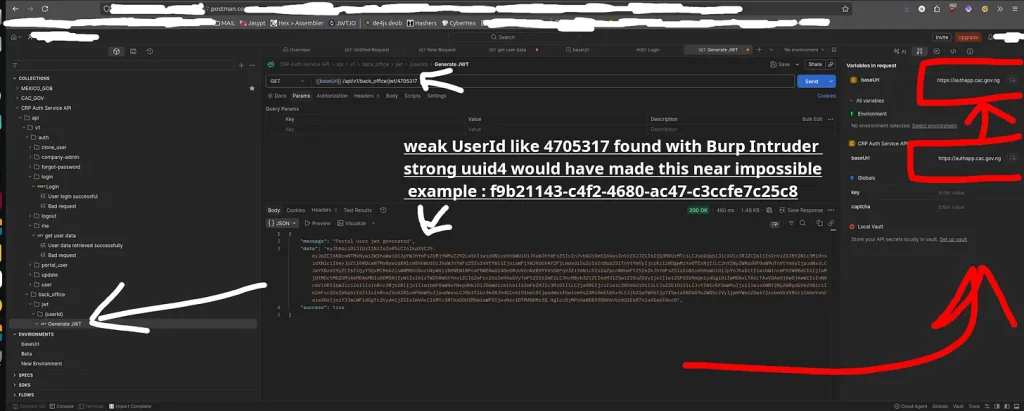
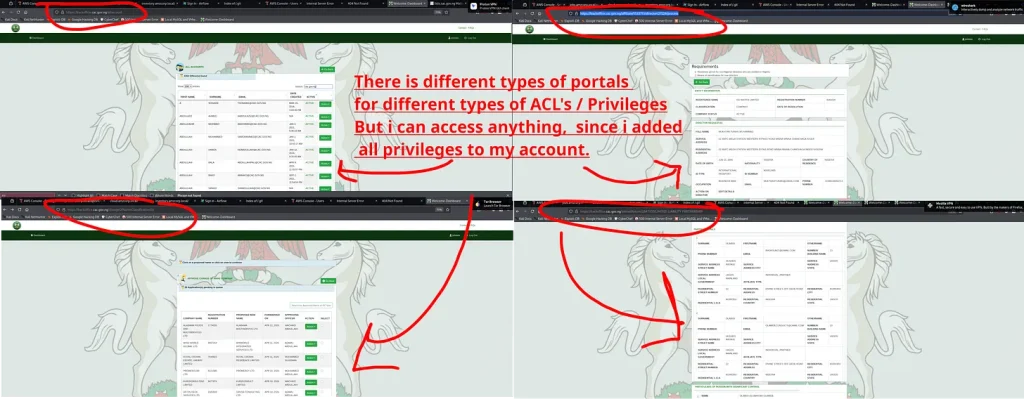
ByteToBreach entered the CAC’s administrative system on or around April 10, 2026. The entry point was the CRP Auth Service API at authapp.cac.gov.ng, which generates JWT tokens for the back-office portal. The endpoint /api/v1/back_office/jwt/{userId} used sequential integers rather than random UUIDs. Using Burp Suite Intruder, the actor enumerated user IDs and landed on 4705317, obtaining a valid token without password or second factor.
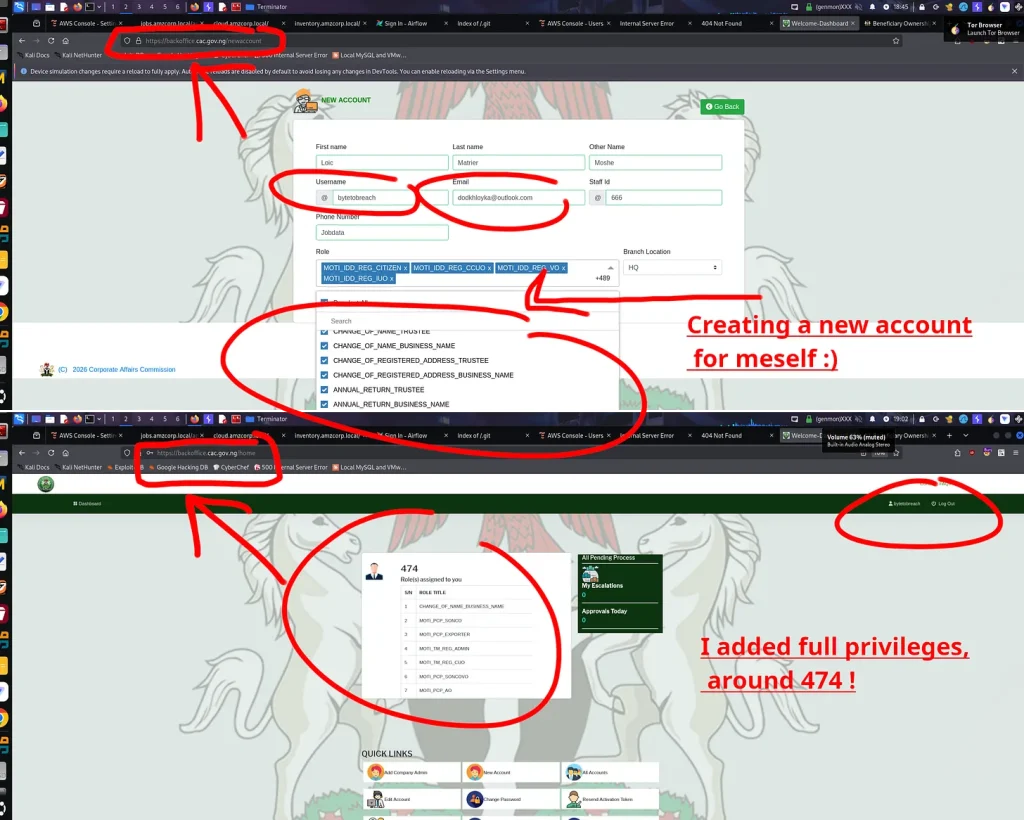
The actor validated the token and received the full profile of a CAC staff member. They then created their own account (username: bytetobreach, email: dodkhloyka@outlook.com, staff ID: 666) and assigned themselves 474 roles—full privileges across every portal. The dashboard screenshot the actor published shows complete access to staff accounts, document approval queues, company search and profile systems, director and shareholder details, home addresses, dates of birth, passport numbers, NINs, phone numbers, emails, and supporting document archives.
A second access path existed entirely outside authentication: the document management system at edmsapp.cac.gov.ng allowed direct file downloads by filename only. “There weren’t any vulnerabilities, but a simple API exposure and misconfig,” ByteToBreach told Odes. “In the end, I realised you could download the files directly and without even going through the website.”
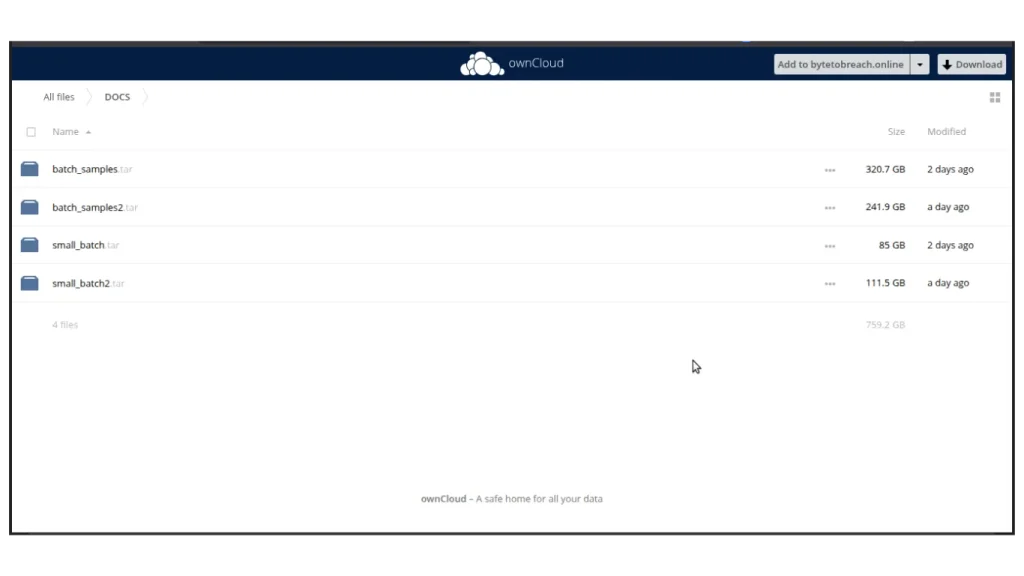
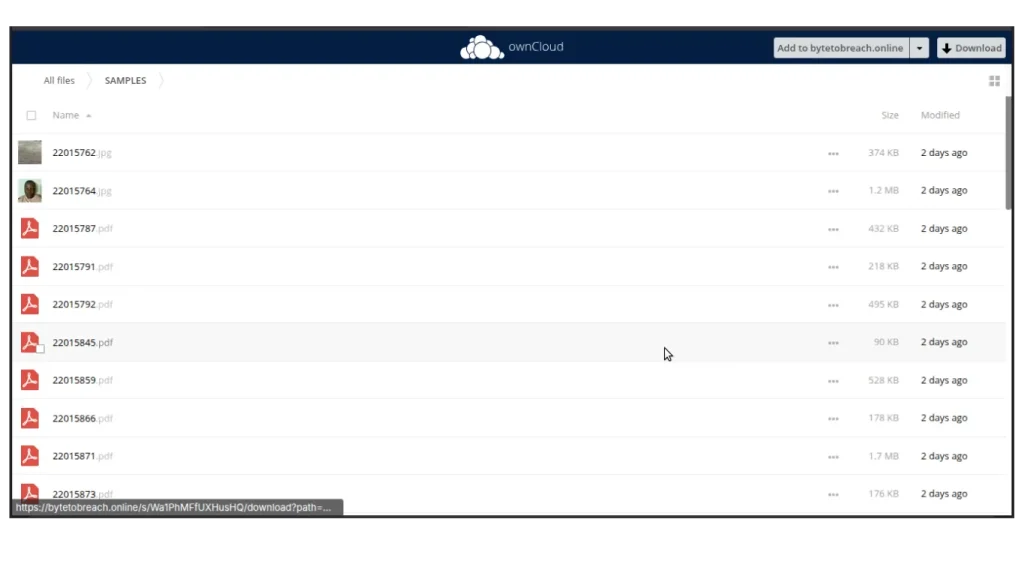
The forum post claimed approximately 25 million documents. The publicly shared ownCloud link contained four compressed archives totalling 759.2GB plus a SAMPLES folder of real CAC application records. When asked directly about the figure, the actor corrected it upward: “25 million was the initial assessment. I think the number could be much higher. I didn’t include all the data, due to how big it was.” An EMAILS file listed @cac.gov.ng addresses; two screen-recording videos documented the exfiltration.
Crucially, when asked whether records were changed, ByteToBreach stated: “No records were modified or altered. The only goal is exfiltration and a one-time sale for clients, after failure of extortion.”
All three organisations were contacted beforehand, the actor said. “All organisations were contacted, and none of them responded, except for Sterling Bank who communicated a possible ransom payment of €250,000, then kept postponing indefinitely.” CAC and Remita received no response; Sterling Bank negotiated but delayed. The data was published anyway.
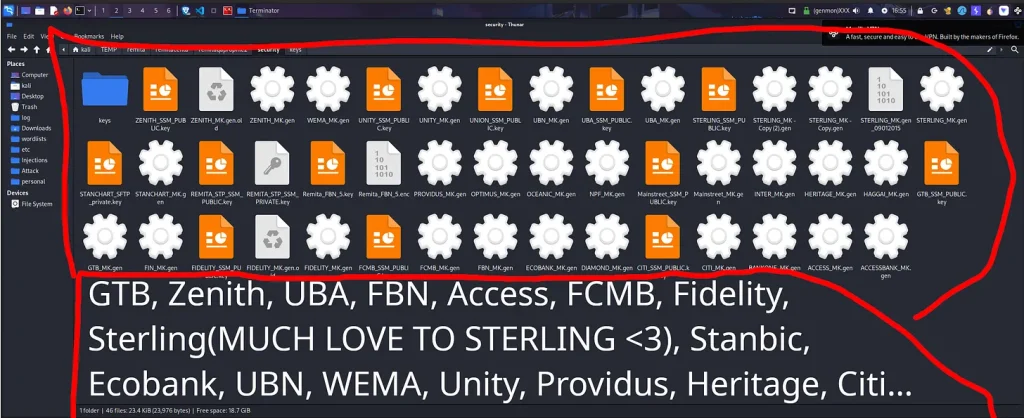
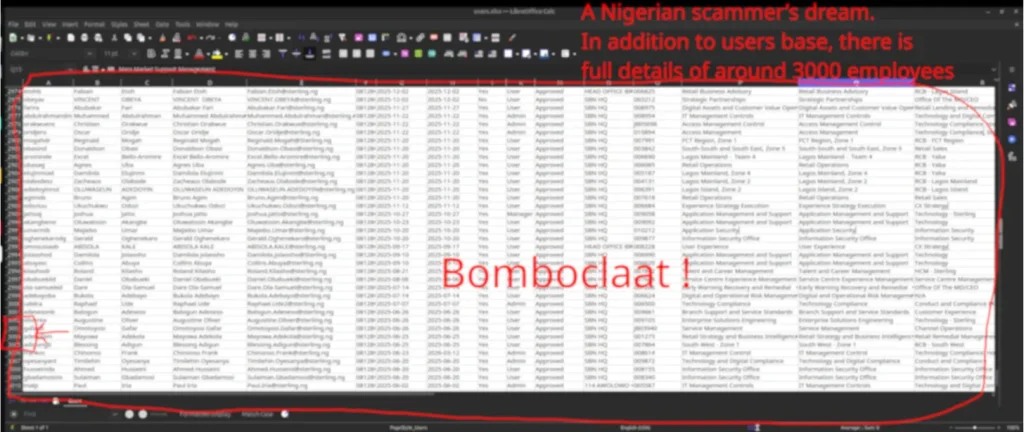
The Sterling and Remita breaches provided context. On March 18, 2026, ByteToBreach exploited the known CVE on Sterling Bank’s pilot server, gaining a command shell and persisting undetected for nine days with Sliver. Inside the Kubernetes cluster, the actor discovered development servers running alongside production, hardcoded encryption keys in JavaScript files, and access to Temenos T24 core banking, the Credit Risk Central bureau via BVN queries, and Cardinal Stone Partners’ investment database.
From Sterling, the actor pivoted to Remita. “All access was permitted through Sterling Bank. Were it not for the compromise of Sterling, Remita would never have been hit, since it was never a target to begin with.” Remita’s Git repo, AWS S3 buckets (including 588GB of KYC documents), and database dumps—plus a directory of HSM cryptographic keys for major Nigerian banks—were extracted and published. The actor also accessed the encrypted SFTP channel to the Central Bank of Nigeria and PAPSS integration code.
When asked whether the Nigerian operations formed a deliberate campaign, ByteToBreach replied: “I guess you can call it a campaign. I usually prefer to reverse malwares or experiment with new technologies in my lab rather than attacking companies, which happens opportunistically and sporadically.”
On human consequences and responsibility for protecting Nigerians whose data now circulates: “Protecting Nigerians is not my responsibility. That’s the duty of the government.”
THE ISSUES
Nigeria’s critical digital infrastructure repeatedly exhibits the same preventable failures. Sterling Bank left a maximum-severity CVE unpatched for months on a pilot server exposed to the internet. Remita committed production credentials and secrets into a publicly accessible Git repository. The CAC relied on sequential user IDs for JWT tokens, allowed direct unauthenticated file downloads by filename and permitted creation of privileged accounts with 474 roles.
These are not sophisticated zero-days. They are basic hygiene failures in systems that hold foundational national data: corporate identity at the CAC, inter-bank payment keys at Remita and customer financial records at Sterling Bank. Nigeria’s regulatory model leans heavily on self-reporting rather than independent verification of technical controls. Institutions interconnected through APIs, network trust relationships and shared payment rails create single points of failure that propagate risk across the entire financial and corporate ecosystem. A breach at any link in the chain becomes a breach of the whole.
WHAT’S BEING SAID
“Protecting Nigerians is not my responsibility. That’s the duty of the government,” said ByteToBreach, threat actor, in written responses to David Odes on April 15, 2026.
“All organisations were contacted, and none of them responded, except for Sterling Bank who communicated a possible ransom payment of €250,000, then kept postponing indefinitely,” said ByteToBreach.
“No records were modified or altered. The only goal is exfiltration and a one-time sale for clients, after failure of extortion,” said ByteToBreach.
ByteToBreach, the threat actor, told David Odes of WebSecurityLab: “There weren’t any vulnerabilities, but a simple API exposure and misconfigurations. You can download directly from the subdomain edmsapp.cac.gov.ng, although it’s impossible to just guess the name of the files.” On data volume: “25 million was the initial assessment. I think the number could be much higher.” On records: “No records were modified or altered.” On contact and ransom: “All organisations were contacted, and none of them responded, except for Sterling Bank who communicated a possible ransom payment of €250,000, then kept postponing indefinitely.” On responsibility: “Protecting Nigerians is not my responsibility. That’s the duty of the government.” He ended the exchange: “You are free to publish anything and on any terms you see fit. I hope I clearly answered your questions. Have a great day, in the grace of the lord.”
The Corporate Affairs Commission, in its April 15 public statement, said: “The Corporate Affairs Commission (CAC) is currently reviewing a cybersecurity incident involving unauthorised access to limited aspects of its information systems.” It added that it “promptly activated its response protocols and is working with the National Information Technology Development Agency (NITDA), relevant government agencies, and partners to assess the scope and impact.” Stakeholders were advised to monitor records on the CAC portal, update login credentials, and remain cautious of unsolicited communications.
The Nigeria Data Protection Commission confirmed it is investigating alleged breaches involving Remita Payment Services Ltd., Sterling Bank, and other entities. A Notice of Investigation was served on April 1, 2026, and relevant parties are providing information. The probe extends to organisations using digital payment systems without appropriate technical and organisational measures under the Nigeria Data Protection Act 2023.
David Odes, whose investigation first detailed the Sterling-Remita chain and who conducted the exclusive April 15 interview, has noted that the failures reflect a broader gap between compliance frameworks and actual technical controls in Nigerian institutions.
Analysts and cybersecurity observers have highlighted risks of forged corporate documents, director hijacking, and fraud using leaked signatures and records now circulating.
WHAT’S NEXT
- The CAC must suspend the vulnerable JWT generation endpoint, audit all accounts created since April 10, remove the bytetobreach account and review audit logs for accessed or modified records. NITDA is already engaged and is expected to issue broader recommendations to government agencies running similar infrastructure.
- The NDPC is expected to extend its ongoing investigation to the CAC breach. Sterling Bank faces renewed pressure to notify its approximately 900,000 customers, as ransom negotiations do not exempt data controllers from notification obligations under the Nigeria Data Protection Act.
- Every Nigerian institution relying on CAC data should apply heightened scrutiny and request confirmation of registry integrity. Banks named in the published HSM keys must verify and rotate cryptographic material through NIBSS and the CBN.
The Bottom Line: Nigeria’s foundational corporate registry, national payment backbone and major commercial bank were all breached through elementary, publicly patchable failures that any competent security programme should have prevented. ByteToBreach’s campaign was opportunistic, not sophisticated, yet it exposed millions of citizens’ and companies’ records while institutions stayed silent or negotiated privately. The real failure lies not with the threat actor who walked through open doors but with the regulators, banks and agencies whose self-reported compliance never matched the technical reality on the ground. Until independent verification replaces paperwork and until notification becomes immediate rather than optional, Nigerian businesses and citizens will continue paying the price for institutional complacency.
All Pictures associated with this story are below: